
LockBit, once heralded as the “world’s most dangerous ransomware” by Europol, has long been a global cybersecurity menace. Operating on a Ransomware-as-a-Service (RaaS) model, this cyber threat orchestrated attacks worldwide, causing billions in damages and making headlines for its audacious approach. However, recent developments signal a turning tide, with international law enforcement agencies collaborating to dismantle this notorious cybercriminal enterprise. This post explores the rise and fall of LockBit, its modus operandi, and the significance of its recent takedown.
LockBit’s RaaS model allowed cybercriminals to leverage its tools and infrastructure, enabling attacks with minimal technical expertise. The ransomware’s global impact was profound, causing billions in damages, and Australia alone suffered millions of dollars in losses. LockBit emerged as the most widely used ransomware globally over the last two years, targeting critical infrastructure with a diverse range of Tactics, Techniques, and Procedures (TTPs), posing a significant challenge to defence mechanisms.
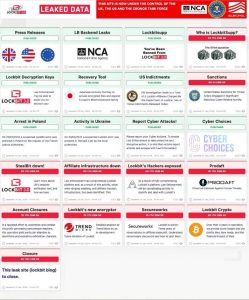
Current LockBit Leak Page
Whilst there is a variance in the TTPs executed by the threat actors using LockBit, the actual ransomware itself has a systematic approach with three identifiable phases:
In summary, LockBit strategically progressed through exploitation, infiltration, and deployment, maximizing the impact of its encryption to coerce victims into ransom payments.
Critical infrastructure, encompassing sectors like energy, transportation, and healthcare, stands as an attractive target for ransomware attackers. The reasons behind this targeting are diverse, with each posing a unique challenge:
In recent years, LockBit ransomware has emerged as a potent and persistent menace, especially when it comes to targeting critical infrastructure. The implications of such attacks extend far beyond financial losses, casting a broad shadow over public safety, national security, and the seamless functioning of essential services.
On February 20, 2024, an international law enforcement coalition, including the NCA, FBI, Europol, and representatives from countries like Australia, France, Germany, and Finland, launched “Operation Cronos” to take down LockBit. The threat group’s site was dismantled, marking a pivotal moment in the fight against cyber threats. Multiple sanctions, arrests, and indictments occurred, with more anticipated. Authorities seized control of the group’s infrastructure, providing the means for victims to decrypt their systems.

Current LockBit Homepage
LockBit, ironically, found itself locked out of its own systems, damaging both its capability and credibility.
US Attorney Philip R. Sellinger for the District of New Jersey affirmed the determination to pursue LockBit’s entire membership, highlighting a global commitment to bring cybercriminals to justice.
US Attorney Philip R. Sellinger for the District of New Jersey
While the fight against cybercrime persists, Operation Cronos stands as a significant step in dismantling high-profile and high-value targets, demonstrating the effectiveness of international collaboration.
Ransomware will almost certainly remain a critical threat to organisations within the Critical Infrastructure sector. Ransomware is an extremely profitable cyber attack method that has surged in the last few years, especially with the emergence of “work from home” and the additional security risks that this provides.
However, the dismantling of the LockBit ransomware group will have significant impacts in the cyber security space. They had previously been one of the most notorious RaaS groups, selling their malware to affiliates and associated cyber criminals and accounting for approximately 26% of ransomware victim organisations since 2022. This had allowed the proliferation of the malware to threat groups who may not have had the capability to achieve this on their own.
It is probable that Operation Cronos has slightly eased the threat for many small to medium sized organisations in the near term with other notorious ransomware groups typically targeting large and profitable companies that they know can pay large ransoms. It is possible that the number of ransomware attacks will decrease in the next 6-12 months as remaining elements of LockBit seek to rebuild the capability.
LockBit’s rise to infamy and subsequent takedown serve as a testament to the collective efforts of global law enforcement agencies in combating cyber threats. While challenges persist, Operation Cronos signifies a significant milestone in the ongoing battle against ransomware and cybercrime, sending a clear message that these threats will not go unchecked.
It is important that you understand the threats facing your organisation and the sector in which you reside. Comprehending the cyber intelligence threat is indispensable for building resilient cybersecurity defences, fostering a proactive security culture, and protecting the interests of individuals, organizations, and nations in an increasingly interconnected digital world.
https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-165a
https://ia.acs.org.au/article/2024/police-decimate-lockbit-ransom-gang-.html
https://www.lepide.com/blog/lockbit-ransomware-everything-you-need-to-know/
https://www.cyberdaily.au/culture/10216-industry-responds-to-lockbit-ransomware-gang-takedown
https://socket.dev/blog/lockbit-takedown
https://www.trendmicro.com/vinfo/au/security/news/ransomware-by-the-numbers/